AI-Powered Memory Safety for C Applications
Created February 2026
Though widely used, including in military systems, applications written in C and C++ are insecure. Adversaries can exploit their temporal memory safety errors to gain unauthorized access, exfiltrate sensitive data, and disrupt system operation.
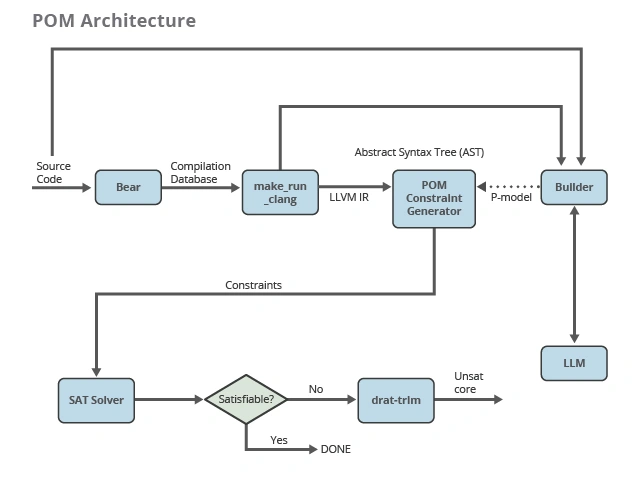
The Pointer Ownership Model (POM) project enforces temporal memory safety. Inspired by Rust's Borrow Checker and C++’s RAII principle, POM can prevent temporal memory safety errors, such as use-after-free errors. It employs a Large Language Model (LLM) and a Satisfiability (SAT) Solver to streamline the generation of models and formal proofs. POM automates the model development process, reducing the time to build a model and achieves 94 percent of pointers modelled correctly by the LLM.
Work With Us
Temporal Memory Safety Bug Detection is Difficult and Costly
Proving the absence of use-after-free errors and other temporal memory safety vulnerabilities is complex and costly, particularly in large codebases such as those for mission-critical military systems. Their intermittent nature frustrates static analysis tools and challenges dynamic analysis tools that find errors only in executed code. Formal methods, which use rigorous mathematical and logical reasoning, offer a powerful approach. However, they require rare skills in mathematical theorem-proving, can take person-years of manual effort, and are difficult to scale.
Preventing improper use after memory has been freed is a key concern. A use-after-free error ensues when memory is de-allocated in the heap (where a program can allocate and deallocate memory) while the program continues to use a pointer to the prior address. This error results in an exploitable vulnerability when attackers access important information allocated to the previously freed memory. Among memory safety errors, use-after-free is second only to buffer overflow in the 2025 CWE Top 25 Most Dangerous Software Weaknesses.
In response to the challenges, CMU SEI enhanced POM, which uses lightweight formal methods for analytical power with scalability. This updated model builds on CMU SEI’s prior POM work that improves C program static analysis for errors involving dynamic memory. Any program that complies with POM can be statically analyzed to ensure that its design is consistent and secure regarding temporal memory safety. POM also leverages technology built in previous CMU SEI projects, Redemption and Detection of Malicious Code. Further, POM stems from a developer’s need to maintain discipline to preserve temporal memory safety in the heap. Based on this observation, the use of POM should be either largely intuitive or provide important secure coding education for C programmers.
Faster Time to Field of Software Free of Temporal Memory Safety Vulnerabilities
With POM, CMU SEI researchers have developed an ownership model used to guarantee memory safety, a builder used to create a per-program ownership model (p-model) for C programs, and a verifier that confirms that the model is consistent and complete, based on builder output and the program source.
In the evaluation test suite, the team has completed a manual POM analysis of the open source dos2unix codebase (version 7.5.2), finding that the LLM (OpenAI’s o4-mini API) correctly labeled 159 of 169 pointers (94.1%).
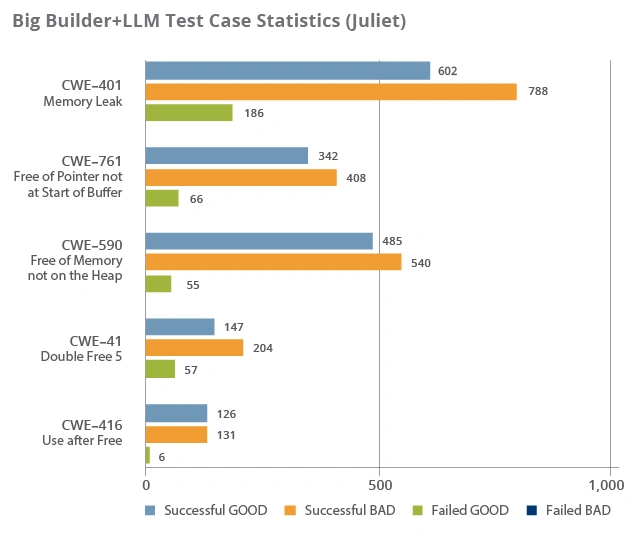
The team also built an API for integrating the LLM into the POM builder and tested it using the Juliet C/C++ test suite with GOOD and BAD code examples organized by Common Weakness Enumeration (CWE). For temporal memory safety code examples CWE-401 (insufficient track and release of allocated memory), CWE-415 (double free error), CWE-416 (use-after-free error), CWE-590 (pointer to memory not allocated using heap allocation), and CWE-761 (pointer not at start of buffer). In our tests, the POM’s LLM-based builder and SAT solver achieved a precision of 99.84% and recall of 83.51%. The top graph shown below is percentage of correct test cases per CWE. The bottom graph is number of test cases in each category in Juliet, where “Successful” indicates that POM correctly either generated a model or reported no model possible, according to whether the code was BAD or GOOD.

Once deployed, POM use will enable faster time to capability for Department of War (DoW) software, because a p-model can be quickly developed and verified for pre-existing software. Specifically, POM will ensure that temporal memory safety vulnerabilities are absent in to-be-fielded software. Mostly an automated process, POM is ideal for deploying artifacts as part of an authority-to-operate (ATO) process.
Consequently, POM results in trustworthy and more resilient software, leading to increased mission assurance. Once built, a valid POM should be easy to maintain as the code evolves. The project's verifier will confirm that the model is sound and complete. Any LLM hallucinations should be caught and reported as errors by the verifier.
Looking Ahead
The POM project demonstrates that LLMs can complete a formal model proving C temporal memory safety.
Future work could investigate how out-of-scope pointers interact with responsible and irresponsible pointers, trace those pointers through integer casts or casts to any other non-pointer types, increase POM’s C language coverage by supporting static pointers and more functions such as 𝚊𝚕𝚕𝚘𝚌𝚊 ( ), or extend temporal memory safety checks to encompass spatial memory safety.
Learn More
Design of Enhanced Pointer Ownership Model for C
•SEI Report
This report describes the design for a new temporal memory safety model for C code and an implementation to enforce it.
ReadUsing the Pointer Ownership Model to Secure Memory Management in C and C++
•Blog Post
Discover the SEI's research initiative to eliminate C/C++ memory management vulnerabilities causing bugs, performance issues, and code execution in this SEI Blog post.
READPointer Ownership Model: Temporal Memory Safety Framework for C
•Collection
The Pointer Ownership Model project aims to deliver a practical, automated framework for enforcing temporal memory safety in C programs.
Learn MorePointer Ownership Model: AI-Powered Memory Safety for C Applications
•Software
The Pointer Ownership Model (POM) project automates enforcement of temporal memory safety for C programs using a Large Language Model and a SAT Solver.
DownloadTemporal Memory Safety in C and C++: An AI-Enhanced Pointer Ownership Model
•Podcast
Lori Flynn, David Svoboda, and Tim Chick discuss recent updates to the modeling framework, Pointer Ownership Model for C.
ListenAI-Powered Memory Safety for C Applications
•Fact Sheet
The SEI pointer ownership model enforces memory safety for use-after-free and other temporal memory safety vulnerabilities.
Learn More